Token health is the new uptime for AI agents

Last week’s most important “agent” product update wasn’t a new reasoning model.
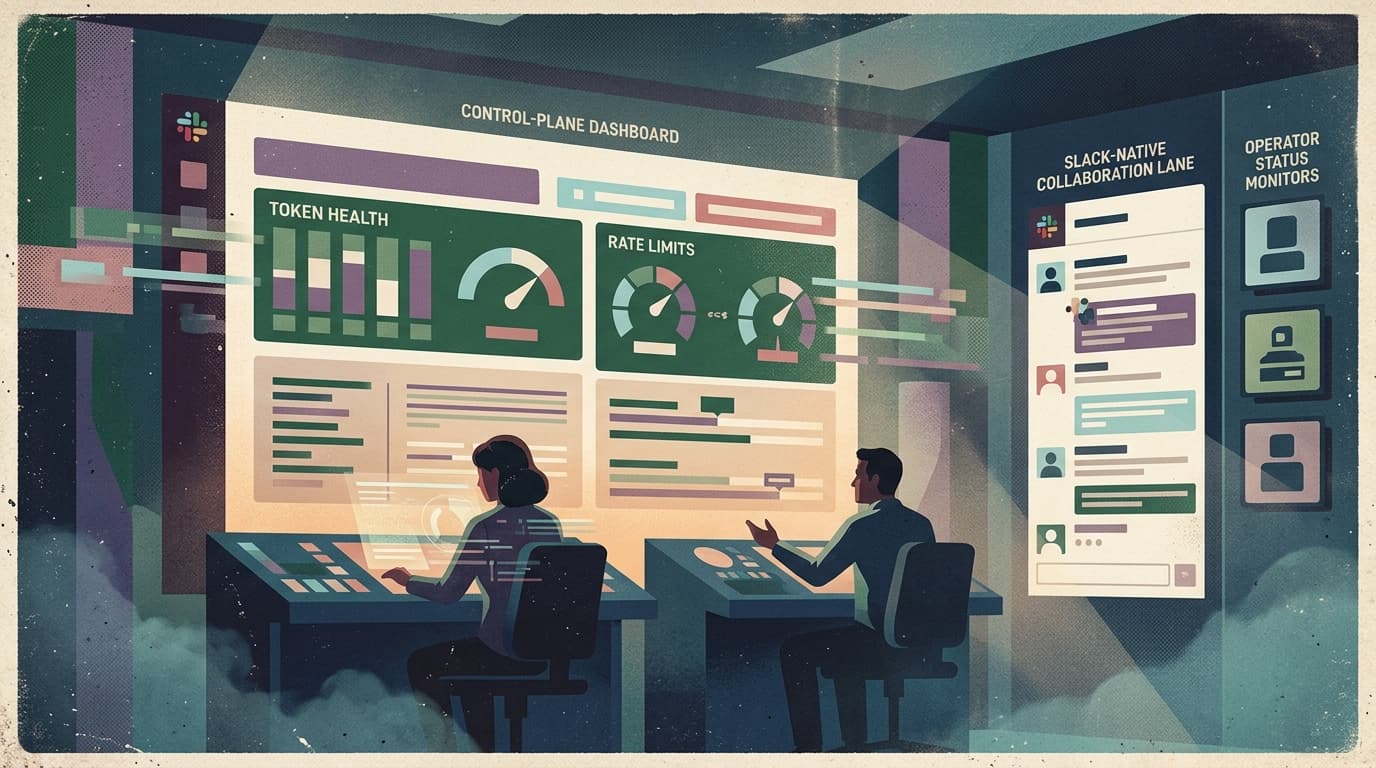
It was a boring dashboard card.
OpenClaw shipped a Model Auth status view that surfaces two things at a glance:
- OAuth token health (expiring, expired, time remaining)
- rate-limit pressure (so you know when you’re about to hit a wall)
If that sounds unsexy, good.
Because this is what decides whether agents become a daily habit inside a team — or a toy people stop trusting.
What changed and why it matters
As teams move from “demo agent” to “agent that touches real work,” the failure mode changes.
The early failure mode is obvious:
- wrong output,
- slow output,
- awkward UX.
The production failure mode is sneakier:
- a token expires,
- a provider silently falls back,
- rate limits spike mid-day,
- a workflow pauses and nobody knows if it’s waiting, dead, or half-done.
That failure feels like this to the buyer:
“We tried the agent thing. It worked… until it didn’t.”
And when reliability is “mysterious,” adoption dies fast.
The market shift is simple: agent products are getting judged like operations products. Not by how clever they are, but by how consistently they keep working.
Main argument: auth and limits are part of your product, not plumbing
Most teams treat auth like setup paperwork:
- connect accounts,
- store tokens,
- forget about it.
That’s fine for a weekend prototype.
In a real team, auth and limits are ongoing conditions, not one-time steps. They’re closer to uptime than to configuration.
If your agent depends on third-party access (models, Slack, Google, Jira, Notion, CRM), then your agent has a heartbeat. And the heartbeat is:
- “do we still have permission?”
- “are we about to get throttled?”
- “did something drift across accounts/profiles?”
The product implication is uncomfortable but clean:
You don’t ship an agent. You ship an operating environment for agents.
If you don’t, your customers will. And they’ll hate you for making them.
Practical implications for founders, product leaders, and ops/growth teams
1) Your onboarding isn’t “connect Slack” — it’s “prove reliability in week one”
The first week sets the narrative.
If a token expires in week one and the user discovers it by seeing silence, you didn’t just ship a bug. You shipped a story:
- “this is fragile,”
- “this will create support tickets,”
- “we can’t depend on it.”
Make token expiry and rate-limit pressure visible before the user feels it.
2) Build an “admin story” before you scale seats
Agents go viral inside companies when they work.
The moment they spread, you need:
- a place an admin can check health in 10 seconds,
- a place they can fix the problem without reading logs,
- a place they can answer: “is it us, or the provider?”
If you don’t give them that, the rollout stops at “cool demo.”
3) Treat fallback behavior as a product decision
Silent fallback sounds helpful (“keep it running”).
But from the buyer’s perspective, silent fallback looks like:
- inconsistent results,
- unpredictable cost,
- unclear blame.
If you do fallback, you need to tell the truth in the UI:
- what provider was used,
- why it changed,
- what the user should do.
4) Pricing and ROI narratives now depend on operational visibility
If customers can’t see why something slowed down or paused, they won’t attribute wins to the system. They’ll attribute misses to it.
Visibility isn’t just reliability — it’s ROI storytelling.
Why this matters for OpenClaw users
OpenClaw is the engine: it makes tool-using, long-running agent workflows real.
But once you run OpenClaw for a team, you immediately inherit team-grade problems:
- multiple providers,
- multiple accounts,
- multiple tokens drifting out of sync,
- rate limits that change day to day,
- and non-technical users who still need a clear answer.
That’s why a shell around OpenClaw matters.
Clawpilot’s job is to make the “boring but fatal” parts operational:
- a real UI that surfaces auth health and provider pressure,
- guardrails so teams don’t unknowingly run on expired credentials,
- and workflows that fail loudly and clearly instead of quietly.
Because the biggest competitor to OpenClaw isn’t another runtime. It’s teams deciding agent automation is too flaky to operationalize.
Closing takeaway
If your agent product feels unreliable, your market doesn’t care whether the model is state-of-the-art.
Treat token health and rate limits like uptime. Then build the shell that makes that uptime obvious — before your users lose trust.