Compaction is now a write path

If you operate agents in production, you already know the most dangerous phrase in the stack:
“We’ll just keep the important bits.”
That sentence usually shows up right before an agent:
- forgets the one instruction that made it safe,
- repeats a week-old incident because it can’t recall the fix,
- or slowly degrades until someone turns it off and calls it “not reliable.”
This week’s signal isn’t a shiny new framework. It’s something more operational: memory is being productized as a platform primitive.
When infrastructure providers ship “Agent Memory” as a first-class service, and memory vendors publish benchmark-driven reports on recall/latency/token tradeoffs, they’re telling you the quiet truth:
Compaction isn’t cleanup anymore. Compaction is a write path.
What changed and why it matters
For a long time, “memory” in agent systems meant one of two bad defaults:
- Stuff everything into the context window (until cost, latency, and quality collapse), or
- Drop history when you compact (until your agent becomes amnesiac and you lose trust)
Even with huge context windows, long-running agents hit the same wall: quality doesn’t scale linearly with more tokens. Past a point, you get noise, contradiction, and “context rot.”
So compaction became normal. But most stacks treated it as a purely internal implementation detail — like garbage collection.
The shift happening now is that compaction is being reframed as an explicit product surface:
- ingestion (what gets extracted),
- storage (where it lives, how it’s isolated),
- retrieval (what comes back, and when),
- and forgetting (what gets removed, and why).
That reframing matters because it changes the operator question from:
- “How big is your context window?”
…to:
- “What exactly are you writing at compaction, and can you prove it?”
Main argument: treat agent memory like production data, not a convenience feature
The fastest way to ship a convincing agent is to add memory. The fastest way to ship a dangerous agent is to add memory with no rules.
The moment memory persists across sessions, it becomes:
- a policy surface (instructions can stick around),
- a privacy surface (user/team data sticks around),
- a security surface (bad data can stick around),
- and a governance/oversight surface (teams will ask who wrote what, when, and why).
In other words: memory becomes production data.
And production data needs production controls.
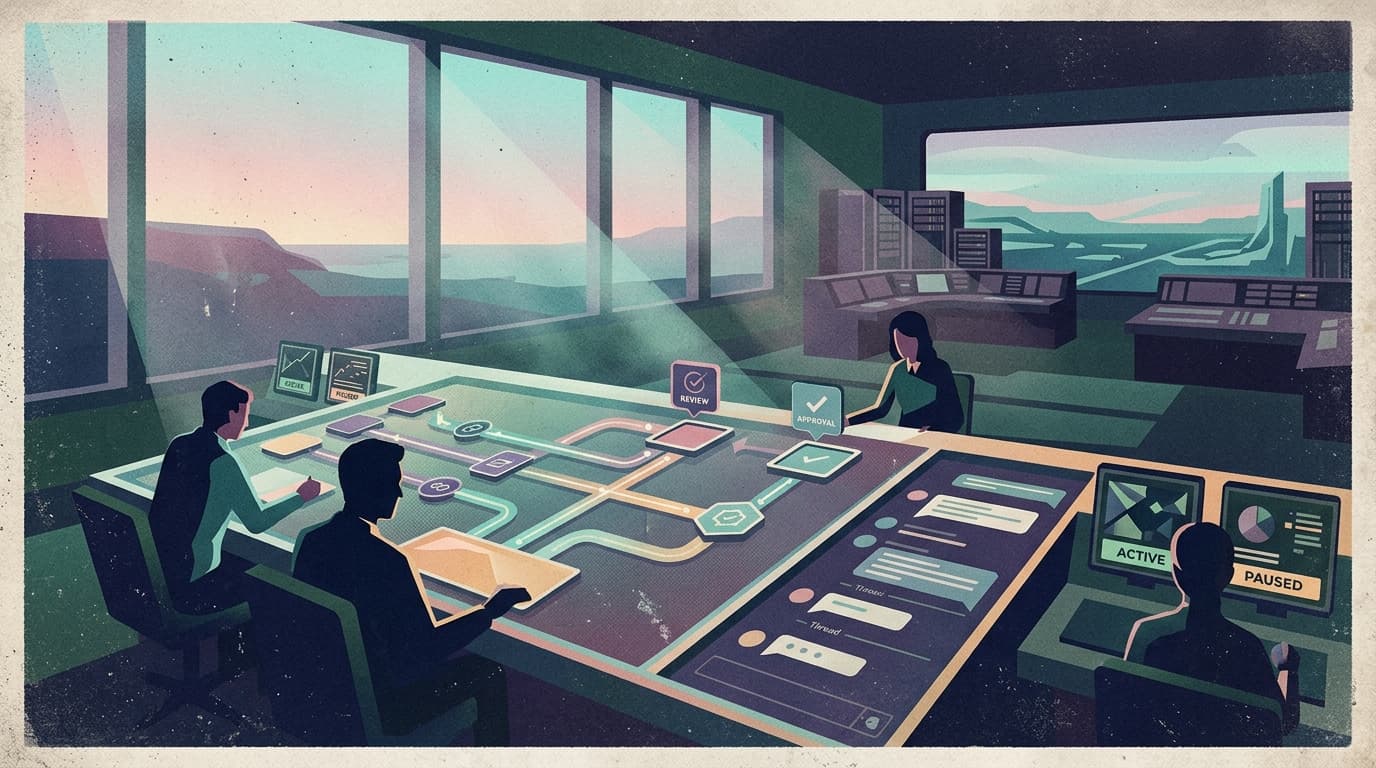
This is where production teams converge: governed speed with safe defaults and calm human oversight.
The non-obvious failure mode: memory turns “one bad turn” into a long incident
Without persistence, most agent failures are ephemeral. You restart, the weirdness is gone.
With persistence, you can get the opposite:
- a wrong conclusion gets stored as a “fact,”
- a subtly unsafe preference gets stored as a “rule,”
- or a transient outage workaround becomes permanent behavior.
Now you don’t have a single bad response. You have a repeating failure.
That’s why “compaction is a write path” is the right mental model. It forces you to ask the same questions you’d ask for any write:
- What schema are we writing?
- Who is allowed to write it?
- What tenant/user/team does it belong to?
- How do we review it?
- How do we roll it back?
Practical implications for builders/operators/teams
1) Add a memory ledger: every persistent memory needs provenance
If a memory influences behavior, you need to know:
- which session it came from,
- which actor wrote it (human, agent, tool),
- and what text triggered the write.
This isn’t bureaucracy — it’s how you debug “why did the agent do that?” without guessing.
2) Separate “facts,” “preferences,” and “instructions” (or you’ll regret it)
Most memory systems store everything as text. Operationally, that’s a trap.
You want at least three categories:
- Facts (things that were true at a time)
- Preferences (user/team defaults that can change)
- Instructions (behavioral rules that should be reviewed like policy)
Because if “use pnpm” and “never touch prod” and “we migrated the database last week” all live in one undifferentiated blob, you can’t govern it.
3) Make forgetting a workflow, not an endpoint
“Forget” is not a button. It’s a process.
Teams will need:
- time-based retention (auto-expire trivial memories),
- incident-driven purges (remove poisoned/incorrect memories),
- and scoped deletion (forget for one user without destroying team knowledge).
4) Memory isolation must match your org boundaries
If you sell to teams, memory should map cleanly to:
- workspace / org
- project
- user
Otherwise you’ll ship the worst kind of bug: not a crash, but a silent cross-tenant leak.
5) Don’t make the model invent its own storage strategy
Letting a model “decide what to save” is fine. Letting a model design your memory system is not.
Operators want an opinionated API and constrained behaviors:
- explicit write operations,
- bounded retrieval,
- deterministic filters,
- and guardrails that don’t burn tokens debating what memory is.
Why this matters for OpenClaw users
OpenClaw makes it easy to build long-running agents with tools, routing, and orchestration. But the minute your agents run for weeks — and the minute a team shares them — memory becomes the difference between:
- a system that gets better over time, and
- a system that accumulates invisible debt.
That’s exactly where a shell around OpenClaw matters.
Clawpilot should be the place you get the boring, essential controls that production memory needs:
- memory profiles scoped to orgs/projects/users,
- an audit trail for every “remember” and “ingest,”
- admin workflows to review and purge memories after incidents,
- and Slack-native control surfaces so humans can correct memory without SSH’ing into anything.
Because the real product isn’t “an agent that remembers.” It’s a team that can trust what the agent remembers.
Closing takeaway
In 2026, memory is no longer a cute feature for demos. It’s becoming infrastructure.
So treat compaction like what it really is:
a write path into production state.
If you operationalize memory like logs and credentials — provenance, isolation, retention, rollback — your agents get safer and more useful over time. If you don’t, you’ll eventually ship an agent that keeps making the same mistake… perfectly.