Your agent needs an ID badge

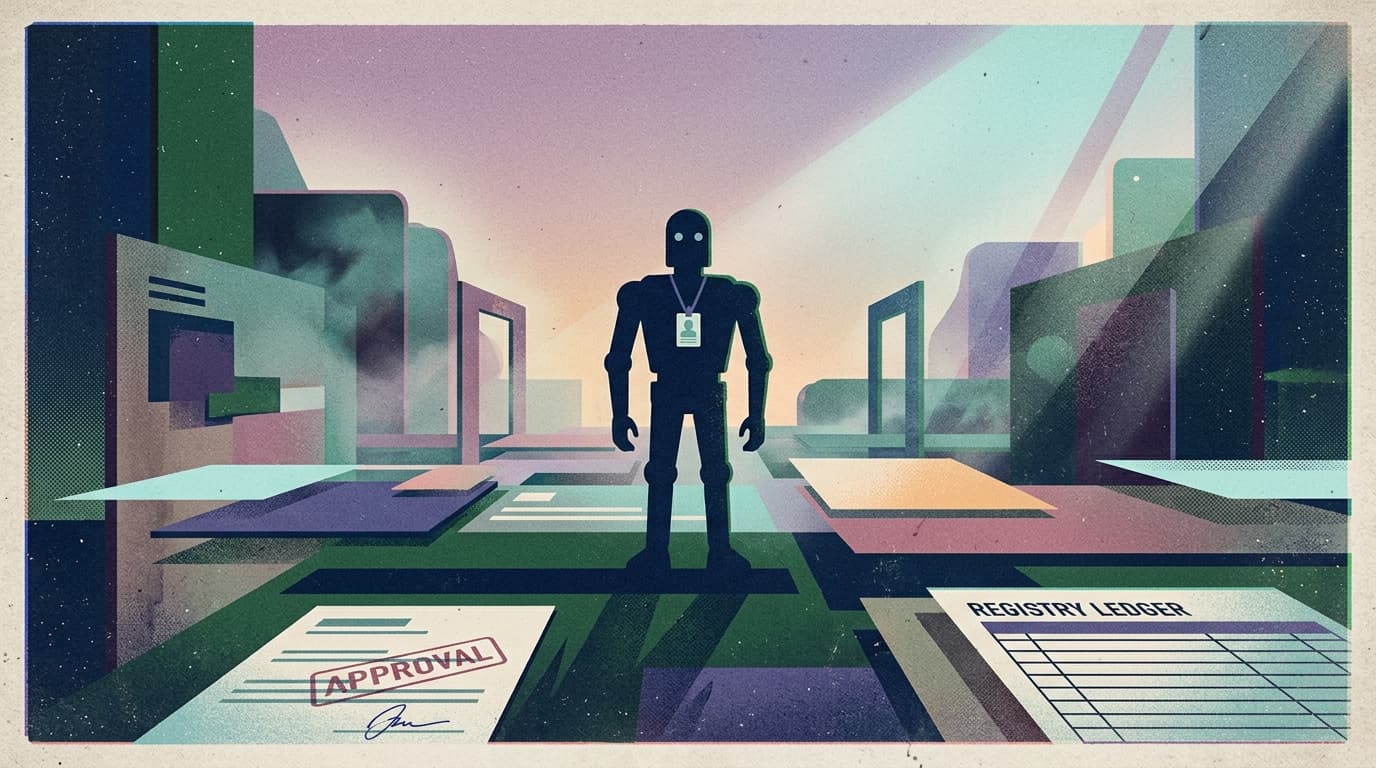
This week’s signal is loud and consistent: the agent story is moving from “wow, it can do things” to “who is allowed to let it do things?”
At Google Cloud Next 2026, the headline wasn’t another model. It was the control plane: Agent Identity, Agent Registry, Agent Gateway, evaluation, simulation, observability.
And in parallel, Workday is explicitly framing agents as first-class citizens with unique identities, scoped authorization, and audit trails—an “Agent System of Record,” not a fun sidecar.
Different companies, same underlying market shift:
Enterprises are treating agents like employees.
Meaning: your agent needs an ID badge.
What changed and why it matters
The first wave of agent products sold on capability:
- it can summarize
- it can draft
- it can run a workflow
That wave hit the enterprise wall fast.
Because the enterprise question is not “can it do the task?” It’s:
- which agent did the task?
- under which identity?
- with which permissions?
- approved by which human?
- producing which audit trail?
- observable in which dashboard when it breaks?
That’s why you’re seeing platforms invest in the boring surfaces (identity, registry, gateway, evaluation) and even put real money behind distribution and procurement support. The center of gravity is shifting from agent intelligence to agent operations.
Main argument: you don’t need “more autonomy”—you need legible accountability
Here’s the stance:
The next competitive advantage in agents is not autonomy. It’s accountability that a buyer can understand.
Founders keep trying to win by pushing the agent further out:
- fewer confirmations
- more background execution
- broader tool access
But that’s upside-down for how real teams adopt.
In a real org, autonomy without legibility creates three immediate outcomes:
- Security says no (or drags procurement for months)
- Ops gets surprise failures (“it said it did it” but nothing happened)
- Leaders can’t defend the spend (“what did we actually automate?”)
So the right product move is to make agent work auditable and governable by default. Not because enterprises hate innovation. Because they hate untraceable outcomes.
Practical implications for founders, product, growth, and ops teams
1) Product: ship an “agent admin story” before you ship more skills
If your product can’t answer these questions in under 30 seconds, you’re not enterprise-ready:
- How do I see every agent that exists?
- What tools can each one call?
- What data scopes does it have?
- What actions are approval-gated?
- Where is the audit log?
- How do I disable it right now?
Your best activation lever isn’t another integration. It’s an admin page that makes risk feel contained.
2) Growth: sell the control plane, not the model
The buyer doesn’t want “Claude vs GPT vs Gemini.” They want:
- predictable rollout
- fewer internal debates
- a clean story to security + legal
- proof the system is doing work, not just chatting
Positioning that wins:
- “agents as non-human teammates with permissions”
- “approvals where it matters”
- “audit trails you can export”
- “observability you can operate”
3) Ops: treat agents like production services (because they are)
If you’re operating agents today, you need the same discipline you’d apply to a critical internal service:
- versioning (what changed?)
- rollbacks (can we revert fast?)
- incident review (why did it act?)
- monitoring (did it execute or just respond?)
The teams that win won’t be the ones with the most prompts. They’ll be the ones with the fewest surprises.
Why this matters for OpenClaw users
If you’re building on OpenClaw, you already have the raw power: tools, workflows, runtimes, providers.
What you need to make it deployable in real companies is the shell around it:
- a place to register agents and manage sprawl
- identity + permissions that map to how teams actually work
- approval gates that match real risk
- audit logs and execution traces you can trust
- an operator experience that makes failures debuggable
That’s what turns “we can run OpenClaw” into “we can run it in our org without fear.”
Clawpilot exists for that exact gap: making OpenClaw practical for teams who have to operate agents, not just demo them.
The takeaway
The market is converging on a boring truth: agents only scale when they’re governable.
If your agent doesn’t have an ID badge, it’s not a teammate. It’s a liability.