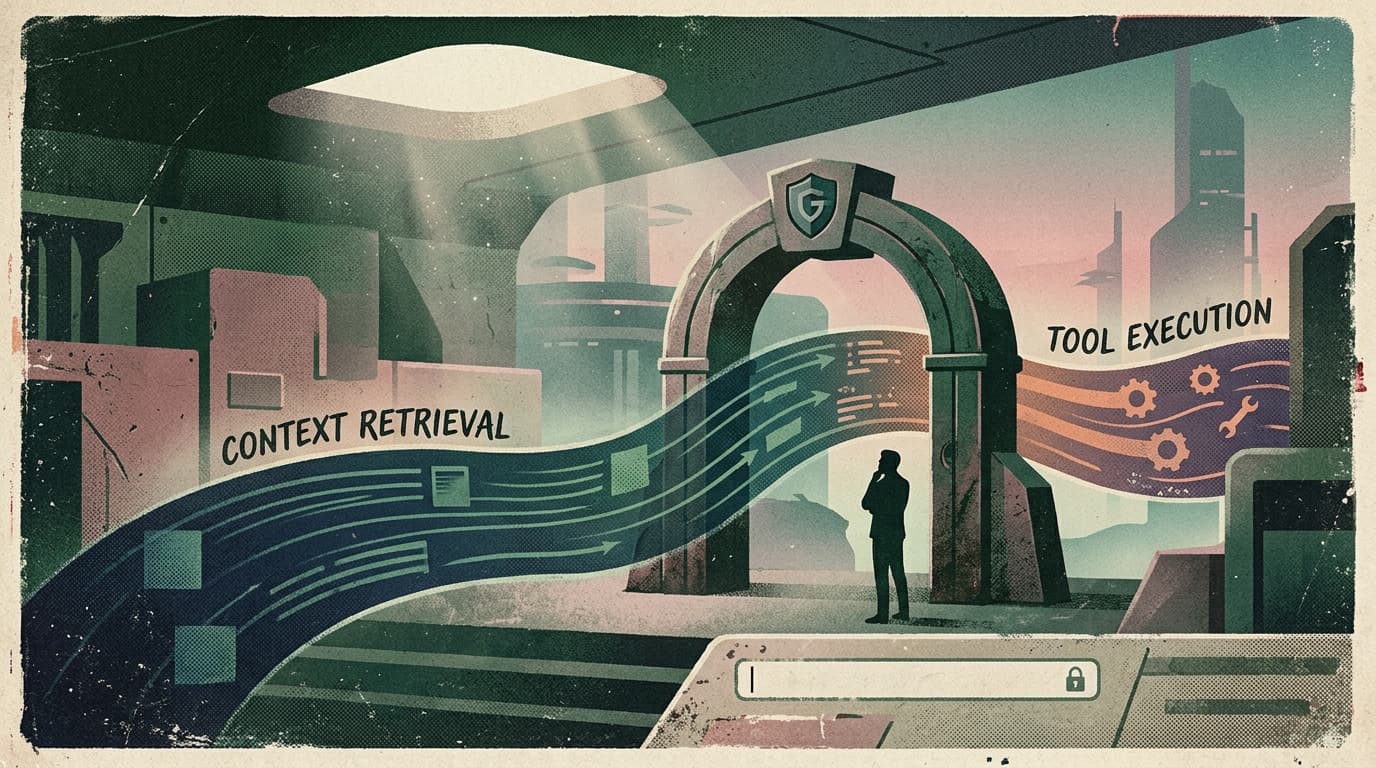
The new moat is permissioned context

Slack just made a very specific bet about what will unlock real agent adoption:
Not “better prompts.”
Permissioned context — and a safe way to act on it.
In their GA announcement for Real-Time Search (RTS) and the Slack MCP server, Slack said they’ve already seen a 25x increase in RTS queries and MCP tool calls since the earlier limited release.
That’s not hype. That’s usage.
And the thing they’re scaling isn’t “chat.” It’s secure context retrieval + execution inside a workplace.
What changed and why it matters
For the last year, most agent products were positioned like this:
- connect tools
- call a model
- do tasks
But inside a real company, “do tasks” is the easy part.
The hard part is everything around it:
- Which conversations is the agent allowed to read?
- Which files is it allowed to reference?
- Which actions are allowed in this workspace, for this person, today?
- How do admins verify it’s not silently becoming a data-exfiltration pipeline?
Slack’s RTS + MCP move is a platform-level admission:
The market is shifting from agent intelligence to agent legitimacy.
When Slack evolves search scopes into granular permission buckets (public vs private vs DMs with consent), they’re telling you where buyers’ heads are:
“Show me exactly what this thing can see, and why.”
Main argument: distribution now runs through governance
Here’s the stance:
The winner won’t be the agent with the fanciest demo. It’ll be the agent that an enterprise admin can approve in under 10 minutes.
Because the real buying path looks like:
- Someone on a team loves the demo.
- IT/security asks what it can access.
- The rollout stalls on scopes, auditability, and uncertainty.
RTS + MCP are meant to remove that stall by making it normal (and expected) that:
- context access is query-based (not “export everything”)
- permissions are user-scoped (not “one big shared token”)
- actions run through a tool layer that can be governed, monitored, and restricted
The implication for founders is uncomfortable but clarifying:
If your agent needs broad access to feel useful, you don’t have a product problem — you have a packaging problem.
Practical implications for founders, product, growth, and ops teams
1) Sell the boundary, not just the capability
The fastest way to lose a buyer is to be vague about what your agent reads and writes.
Treat your permission model like a feature:
- “This is what it can see.”
- “This is what it can do.”
- “This is what it can’t do, even if asked.”
If you can’t explain that in plain English, you’re not enterprise-ready.
2) Make “context onboarding” a first-class flow
Most teams don’t fail because the model is wrong. They fail because the agent has:
- too little context (so it hallucinates or guesses), or
- too much access (so it becomes unshippable)
Your onboarding should deliberately answer:
- Which channels/projects should the agent watch?
- What’s the default retrieval behavior (narrow vs broad)?
- What’s the escalation path when it can’t find enough signal?
3) Design for “retrieve small, act small”
RTS is a signal that buyers want tight retrieval loops.
So don’t build agents that need to ingest everything to be useful. Build agents that:
- fetch the minimum context needed
- produce a reviewable artifact
- take a constrained action
- leave a trail
That’s how you get from “cool pilot” to “daily workflow.”
4) Your go-to-market pitch needs an admin story
Your champion isn’t enough.
You need a version of your pitch that’s explicitly for:
- workspace admins
- security reviewers
- ops owners
It should cover:
- permissions and scopes
- audit logs
- kill switches / controls
- how you prevent accidental data sprawl
If you don’t have this, you’re forcing your champion to invent it. And they won’t.
Why this matters for OpenClaw users
OpenClaw is great at building real agents — ones that can plan, call tools, and run work.
But as Slack’s RTS + MCP push makes clear, the thing that determines whether an agent ships isn’t cleverness. It’s whether you can run it with:
- permissioned context (the agent sees what the user is allowed to see)
- governed tools (the agent can only do what the org allows)
- operational controls (logs, approvals, and safe defaults)
That’s exactly where a “shell around OpenClaw” matters.
Clawpilot isn’t just about hosting an agent runtime. It’s about making OpenClaw deployable in real teams — with the boring-but-essential admin layer that turns agent prototypes into day-to-day operations.
Closing takeaway
The next wave of agent winners won’t win because they’re the smartest.
They’ll win because they’re the easiest to trust.
If you’re building in this space, stop treating context and permissions as plumbing. Treat them as the product.