Multi-agent orchestration just became a governance problem

The last 48 hours made one thing painfully clear: everyone wants multi-agent systems, but almost nobody is talking enough about runtime control.
On April 2, Microsoft pushed two signals at once: broader multi-agent orchestration capabilities in Copilot Studio, and a separate open-source Agent Governance Toolkit focused on enforcing policy at runtime. That pairing is the real story.
Not “agents are smarter.” Agents are now connected enough to break things faster.
What changed and why it matters
For months, teams treated orchestration as a capability milestone: more agents, more tools, more delegated tasks.
Now platform vendors are saying the quiet part out loud:
- orchestration is going GA,
- open Agent-to-Agent collaboration is a requirement,
- and governance has to move into the execution path, not sit in docs.
That is a market maturity signal. When vendors start shipping policy engines, trust layers, and deterministic enforcement claims next to orchestration features, they are admitting that production failures are mostly coordination failures, not model IQ failures.
Main argument: your agent architecture is now a control system, not a prompt system
Here’s the opinionated take: if your multi-agent stack cannot answer “who approved this action, under what policy, and where is the kill switch?” in seconds, you are not running production AI.
You’re running a demo with a pager.
Single-agent apps can hide weak governance for a while. Multi-agent systems can’t. As soon as one agent can delegate to another across tools and data boundaries, your blast radius jumps:
- wrong delegation becomes cross-system damage,
- vague identity becomes privilege confusion,
- retry loops become expensive cascading failures,
- and weak observability becomes postmortem fiction.
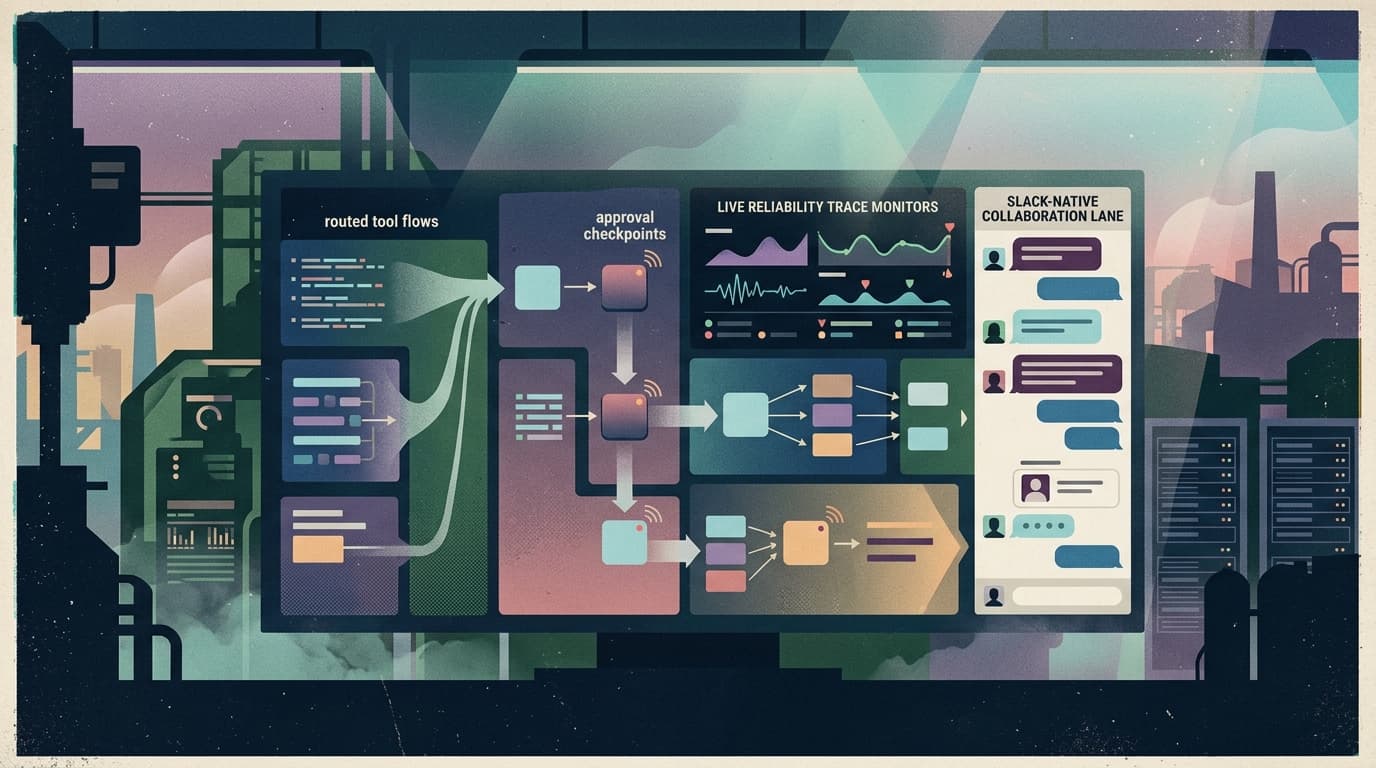
So the practical stack order has flipped:
- control plane,
- policy + identity,
- observability + rollback,
- then orchestration quality.
Most teams still build this in the opposite order. That is why pilots look great and rollouts stall.
Practical implications for builders, operators, and teams
Builders
Treat every tool call like a privileged syscall. Define explicit contracts for:
- who can call what,
- max scope of action,
- what requires human approval,
- and what auto-fails closed.
“Agent autonomy” without policy contracts is just permission debt.
Operators
You need runtime posture, not dashboard vibes. At minimum:
- action-level audit trails,
- per-agent budgets and circuit breakers,
- delegation traces across agent hops,
- and one-click suspension when behavior drifts.
If you can’t freeze or route around a bad agent quickly, you don’t have operations. You have hope.
Teams and adoption owners
Your rollout plan should be staged by trust tier, not by feature list.
- Tier 1: read-only workflows
- Tier 2: reversible writes with approval
- Tier 3: bounded autonomous actions
This reduces legal, security, and change-management friction because you can prove containment before expanding authority.
Why this matters for OpenClaw users
OpenClaw gives you the runtime flexibility to build serious multi-agent workflows. That’s power. But once those workflows touch real systems, power without control becomes operational drag.
This is exactly where a shell around OpenClaw matters.
Clawpilot’s job is not to replace OpenClaw’s openness. It’s to make that openness deployable for real teams: managed hosting, operator-friendly controls, and Slack-native access where people already coordinate work.
In practice, that means teams can keep OpenClaw’s capability while getting a cleaner path to governance, rollout, and day-2 operations.
Closing
The market is done asking whether agents can do work. Now it’s asking whether agent systems can be governed when that work goes sideways.
The winners will not be teams with the flashiest orchestration graph. They’ll be teams with the best control surface when the graph misbehaves.